AS/400 (IBM iSeries, AS/400e, eServer iSeries/400, Power Systems)
What is the AS/400 (IBM iSeries, AS/400e, eServer iSeries/400, Power Systems)?
The IBM Application System/400 -- or AS/400 -- is a family of midrange computers that was released in 1988, succeeding both System/36 and System/38 platforms. The first generation of AS/400 was based on a 48-bit complex instruction set computer (CISC) and ran the OS/400 operating system. The AS/400 was subsequently rebranded as the AS/400e, eServer iSeries, eServer i5 and System i. It is now Power Systems.
The AS/400 system came with an integrated relational database management system known as Db2. It used technology independent machine interface (TIMI), a platform-independent instruction set architecture (ISA) that made it possible to change the underlying processor and still run the same applications.
Before the mid-1960s, the only computers that were available for businesses were mainframes, which only the biggest companies could afford to own and operate. During the late 1960s and early 1970s, midrange computers became widely available, enabling most medium-sized organizations to own their own computer. At the time, these systems were also known as minicomputers.
As microcomputers emerged in the late 1970s and early 1980s, midrange systems filled the niche between mainframes and microcomputers. In the late 1980s, IBM dominated both mainframe and microcomputer markets and began to take a more aggressive approach to the midrange market by improving on its midrange System/36 and System/38 platforms.
Shortly after launching the AS/400 in 1988, IBM quickly established its newest midrange system as an advanced business computer, competing with Digital Equipment Corp. and Hewlett-Packard. By 1997, IBM had already sold almost half a million AS/400 systems.
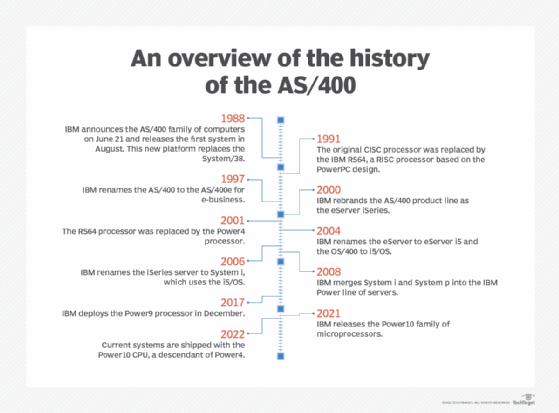
A history of the AS/400 overhauls and rebranding
Since its initial launch, the AS/400 has undergone the following overhauls:
- In 1991, the CISC processor was replaced by a 64-bit reduced instruction set (RISC) processor, called the IBM RS64, which was based on the PowerPC design. PowerPC was a RISC ISA created by the 1991 Apple-IBM-Motorola alliance, known as AIM.
- In 2001, the RS64 processor was replaced by the Power4 processor.
Thanks to the use of TIMI, the platform remained backward compatible despite the change of processors -- even when the move was made from CISC to RISC. The AS/400 and many of its components have also undergone the following series of brand and packaging changes:
- In 1997, the platform was renamed AS/400e, with the "e" emphasizing e-business as a target category of use cases.
- In 2000, the product line was renamed eServer iSeries. It became a part of the eServer family of platforms, along with pSeries, which was based on the same CPU -- the Power4 processor starting in 2001. The hardware of the subsequent version of iSeries and pSeries platforms became virtually identical. But the two systems ran different operating systems: iSeries ran OS/400; pSeries ran AIX, an operating system developed by IBM based on Unix.
- In 2004, the eServer began using Power5 processors and was renamed eServer i5. At the same time, OS/400 was renamed i5/OS.
- In 2006, eServer i5 became known as System i.
- In 2008, IBM merged System i and System p into a single product line, called IBM Power servers. i5/O5 was rebranded as IBM i, where "i" stands for integration.
The hardware platform originally marketed as the AS/400 has evolved into the systems that are now known as IBM Power servers, which are part of the larger family of products called IBM Power Systems. The current systems are shipped with the Power10 CPU, a descendant of Power4. What was originally marketed as the OS/400 operating system is now called IBM i. Power servers are sold with the IBM i operating system but also with two other operating systems: AIX and Linux.
Is the AS/400 still being used?
Companies that haven't upgraded to more modern systems still use AS/400. The same is true for AS/400e, eServer iSeries eServer i5 and System i platforms. These older systems are often used with resource-intensive applications, such as enterprise resource planning, banking and medical information systems.
The hardware underlying all these systems evolved into a product line that's now known as IBM Power servers, named after the Power processors they're based on. The most recent generation of Power servers uses Power10 processors and some can be packaged with three different operating systems: IBM i -- formally OS/400 -- AIX, and Linux.
IBM markets IBM i as an environment that integrates an operating system with a database, virtualization layer, application server and transactional system. The systems are built to reduce downtime and support costs. The operating system can be deployed on Power Systems hardware or in the cloud.
A white paper published by IBM on May 3, 2022, lists the following uses of IBM i running on Power servers:
- Data management. IBM i includes a fully integrated database, Db2, which provides database-record-level access and standards-based SQL.
- Software development. IBM i offers some of the more traditional development languages, such as RPG, COBOL, C, C++ and Java. It also provides more modern open source languages, tools and environments for applications such as artificial intelligence (AI) and internet of things (IoT).
- AI. IBM i provides access to IBM Watson through open source technology.
- IoT. IBM i provides access with IoT applications through open source interfaces.
Learn how IBM Power systems are giving organizations more options for deploying hybrid cloud and a new pricing model.
